Pakistani government websites hacked on 70th Independence Day
August 14, 2017India and Pakistan hit by Malware – “State-sponsored” cyber espionage campaign
August 29, 2017Recently, the Tier3 team has seen ransomware being used in attacks targeting WordPress sites in Pakistan. We are currently tracking a ransomware variant experts are calling “EV ransomware.”
Ransomware is malicious software that an attacker installs on your computer or on your server. They use an exploit to gain access to your system, and then the ransomware executes, usually automatically.
Ransomware encrypts all your files using strong unbreakable encryption. The attackers then ask you to pay them to decrypt your files. Usually payment is via bitcoin. Bitcoin gives the attackers a way to create an anonymous wallet into which the ransom can be paid.
Ransomware has been around for a long time. It originally dates back to 1989 with the “PC Cyborg trojan horse virus” that would extort its victims into sending $189 to a PO Box in Panama to get their files decrypted. The encryption on that virus was easily crackable.
Ransomware today is growing fast. In 2017, 100 new ransomware variants were released into the wild, and there was a 36% year-over-year increase in ransomware attacks worldwide. The average ransomware demand increased 266% to an average of $1077 per victim. [Source: Symantec Threat Report 2017]
This year we have seen ransomware attacks on a scale that would have been hard to imagine several years ago. In May of this year, the WannaCry ransomware attack affected hundreds of thousands of people in over 150 countries. The UK National Health System was affected and had to divert ambulances away from affected hospitals.
In June we saw the Petya (eventually dubbed NotPetya or Netya) ransomware rapidly spreading, starting in Ukraine. A large number of high-profile organizations were affected, including Ukraine’s state power company, the Chernobyl nuclear reactor, Antonov aircraft, shipping company Maersk and food giant Modelez.
Today a large number of affected people and organizations actually pay attackers when they are hit by ransomware, and sometimes their files are successfully decrypted. Security organizations, including the FBI, generally advise customers to not pay attackers because this encourages the spread of this kind of attack. However, many organizations simply do not have the option of not recovering their data – and so they pay, which perpetuates this criminal business model.
Most ransomware targets Windows workstations. However, the Tier3 team is currently tracking an emerging kind of ransomware that targets WordPress websites.During our analyses of malicious traffic targeting Pakistani websites, we captured several attempts to upload ransomware that provides an attacker with the ability to encrypt a WordPress website’s files and then extort money from the site owner.
The ransomware is uploaded by an attacker once they have compromised a WordPress website. It provides the attacker with an initial interface that looks like this
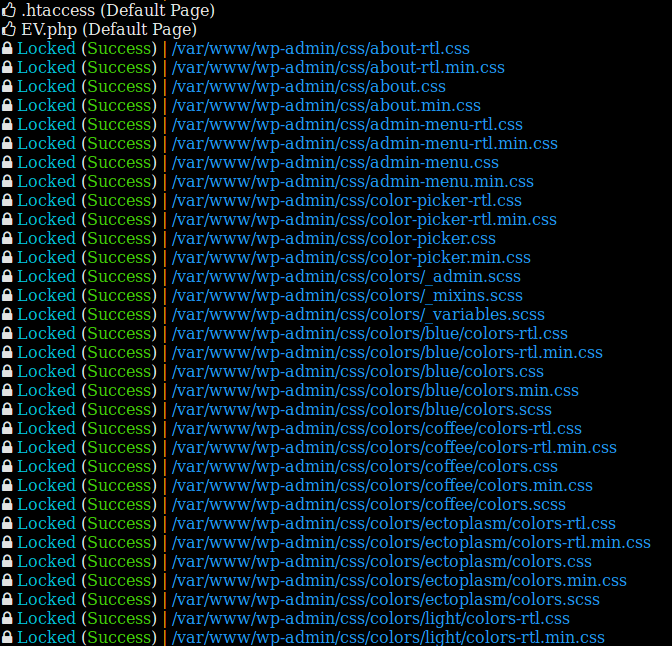
The ransomware will not encrypt files that have the following patterns:
*.php*
*.png*
*404.php*
*.htaccess*
*.lndex.php*
*DyzW4re.php*
*index.php*
*.htaDyzW4re*
*.lol.php*
For each directory that the ransomware processes, it will send an email to its owner which was “[email protected]” for this specific build ,it informs the recipient about the host name and the key used to perform the encryption.
All files affected are deleted and another file takes their place with the same name, but with the “.EV” extension. This new file is encrypted.
The version we discuss in this post only affects files. Tier3 suspects that soon a ransomware targeting the DB within a few months. It’s such an obvious high value target. Probably the wp_users table would be the first thing to go after – encrypting just the email column would be very destructive. A site would essentially be disabled and have no way to communicate with customers until the ransom is paid.
An additional layer of protection against a ransomware attack is to ensure that you have good offline backups. Make sure your backups don’t live on your web server. They need to be backed up to a separate server or a cloud storage service like Dropbox or Google Drive.
Keep in mind, though, that your backups are your last line of defense. It is better to avoid getting hacked in the first place.