Ransomware Attack
If you need help Identifying the type of ransomware which has affected your system and encrypted your files then Tier3 Pakistan provides this service FREE for our customers and other internet users in Pakistan. We maintain more than 700 ransomware virus signature in our database which is constantly updated. Please fill out the form with required information start the identification process.
To help us define the type of ransomware affecting your device, please fill in the form. This will enable us to check whether there is a solution available. If there is, we will provide you with the link to download the decryption solution.
* For our local and less tech savvy customers we provide support and help in Urdu Language.
Ransomware Decryption , removal and negotiation Services
- Ransomware Readiness Assessment Plan.
- Technical analysis of the ransomware.
- Development of a decryption tools whenever possible.
- Work out the best data recovery strategy
- As a last resort Ransom Negotiation, Transaction handling and recovery assistance with less chance of data loss for our customers in Pakistan.
- Fine-tuning and hardening your security
Ransomware Negotiations
Most people have never dealt with a cyber criminal and we would never recommend doing so without professional help. Negotiating with them directly can often make situations worse and also compromise your security. Bitcoins are required to pay the ransoms and can be difficult to obtain. Should paying the ransom be the last resort, please seek an experienced Ransomware removal experts and consultant in Pakistan to deal with the cyber attacker and recover your data on your behalf.
Our expert negotiators have extensive experience resolving ransomware attacks, including arranging the destruction of exfiltrated data to reduce the damage caused by dual ransomware/data theft attacks.
We also provide comprehensive services for organisations and corporates in Pakistan. These services include evaluating and confirming attacks, and conducting post-attack remediation activities including executive support at board meetings, legal counsel, coordinating with insurance companies, public relations messaging and execution, and communications with key stakeholders including investors, employees and customers.
Ransomware Readiness Assessment
Tier3 Ransomware Readiness Assessment Plan can help organizations identify and mitigate vulnerabilities and weaknesses that could make them vulnerable to ransomware attacks. It also provides a structured approach to improving overall cybersecurity posture. A Ransomware Readiness Assessment plan is a critical component of an organization's cybersecurity strategy to evaluate its preparedness for ransomware attacks.
Paying the Ransom?
Although ethically Tier3 advises against paying the ransom. However, if you are considering it, you will need a team with specialized skills to help you. Additionally, paying the ransom or working out a settlement is not going to remediate the vulnerabilities that the attackers exploited, so it's still essential to identify the initial access point and patched the vulnerabilities. Everything you say or don’t say, the communication channels you use, and the timing and tone of your communications will all have a bearing on these proceedings. Structuring the deal, the money transfer, and the data recovery are critically important. Leverage the expertise of our ransomware negotiator to safely handle the cyber attackers.
Our ransomware removal experts can help you sanitize systems or create new builds. When rebuilding or sanitizing your network, we ensure the appropriate security controls are installed and our team follows best practices to ensure your devices do not become reinfected. We help you review your ransomware incident response with our Ransomware Readiness Assessment plan to understand what went right or wrong and to document opportunities for improvement. Our technical experts can help you deploy attack surface reduction (ASR) rules ensuring the continuous improvement of your response and recovery capabilities for the future. 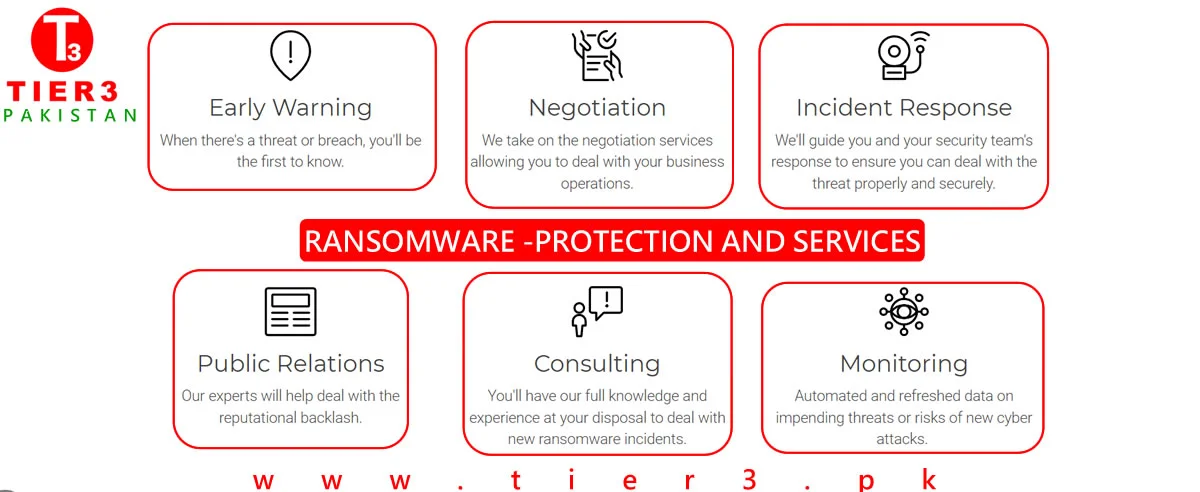
Ransomware Attack in Pakistan
Ransomware Attack In Pakistan - FAQs
More advanced malwares encrypt the victim's files, making them inaccessible, and demands a ransom payment to decrypt them.[1] The ransomware may also encrypt the computer's Master File Table MFT or the entire hard drive. Thus, ransomware is a denial-of-access attack that prevents computer users from accessing files since it is intractable to decrypt the files without the decryption key. Ransomware attacks are typically carried out using a Trojan that has a payload disguised as a legitimate file.
famous examples of ransomware are creber, netwalker, locky, REvil, cryptolocker, spora, Lockbit, WannaCry etc.
- Infection: Whether through a phishing email, physical media (e.g. USB drive), or any other method, the ransomware need only install itself on a single endpoint or network device to gain access.
- Secure Key Exchange: Once installed, the ransomware sends a signal to the perpetrators / attackers central command and control server to generate the cryptographic keys that will lock your system.
- Encryption: With crypto lock in place, the software will begin encrypting any files it can find, both on the local machine and across the network.
- Extortion: Now that it has gained secure and impenetrable access to your files, the ransomware will display an explanation of what comes next details of the exchange, the ransom amount, and the consequences of non-payment.
- Unlocking or restoring: At this point, the victim can either attempt to remove infected files and systems and restore from a clean backup, or pay the ransom. If you are forced to pay, negotiating is always an option, remember average payments generally ran 42.87% of what was initially asked.
Attackers leverage ransomware to get your attention and get you to act on a deadline. Have a backup? They’ve overcome it and still they’ll post your data for all to see if they don’t get their money. Sometimes they expose your data without a ransomware attack, but the sight of locked-up computers and zero business going on means you have to act - NOW!
They might just forgo the ransomware and go straight to extortion.
Paying the ransom is never recommended, mainly because it does not guarantee a solution to the problem. There are also a number of issues that can go wrong accidentally. For example, there could be bugs in the malware that makes the encrypted data unrecoverable even with the right key.
In addition, if the ransom is paid, it proves to the cyber criminals that ransomware is effective. As a result, cyber criminals will continue their activity and look for new ways to exploit systems that result in more infections and more money on their accounts.
A ransomware attack is typically delivered via an e-mail attachment which could be an executable file, an archive or an image. Once the attachment is opened, the malware is released into the user’s system. Cyber criminals can also plant the malware on websites. When a pakistani user visits the site unknowingly, the malware is released into the system.
The infection is not immediately apparent to the user. The malware operates silently in the background until the system or data-locking mechanism is deployed. Then a dialogue box appears that tells the user the data has been locked and demands a ransom to unlock it again. By then it is too late to save the data through any security measures.
Any Pakistani consumer and any Pakistani business can be a victim of ransomware. Cybercriminals are not selective, and are often looking to hit as many users as possible in order to obtain the highest profit. This is why we suggest all internet users to have enabled their systems ransomware protection and always keep backup of their data. Please remember - default security softwares (Windows defender etc) that come bundled with your Operating system are not enough to protect you from growing lists of malware threats. It is always advisable to purchase a specialised anti virus or anti ransomware solution to protect your systems and networks from cyber and ransomware attacks.
Yes, because cyber criminals know that organizations are more likely to pay as the data held captive is typically both sensitive and vital for business continuity. In addition, it can sometimes be more expensive to restore backups than to pay a ransom.
Tier 3 has seen a sudden spike in businesses being affected from ransomware specially with growth in Crime-as-a-Service (CaaS) and most of the time there is no back up or any cyber security policy which is being implemented. Tier 3 is always happy to help its valuable clients in Pakistan with post- attack services which include system cleansing, data backups, malware analysis, identify attack vector or forensics. Please feel free to contact us if you have require any more information.
Ransomware infections occur in different ways, such as through insecure and fraudulent websites, software downloads and malicious attachments. Anyone can be a target – individuals and companies of all sizes.
Fortunately, there are ways for you to be prepared and reduce the likelihood of finding yourself in front of a locked laptop or encrypted file. You can significantly reduce the chances of infection by applying security steps and paying attention online.
Ransomware is on the rise – there are now more than 50 families of this malware in circulation — and it’s evolving quickly. With each new variant comes better encryption and new features. This is not something you can ignore!
One of the reasons why it is so difficult to find a single solution is because encryption in itself is not malicious. It is actually a good development and many benign programs use it.
The first crypto-malware used a symmetric-key algorithm, with the same key for encryption and decryption. Corrupted information could usually be deciphered successfully with the assistance of security companies. Over time, cybercriminals began to implement asymmetric cryptography algorithms that use two separate keys — a public one to encrypt files, and a private one, which is needed for decryption.
The CryptoLocker Trojan is one of the most famous pieces of ransomware. It also uses a public-key algorithm. As each computer is infected it connects to the command-and-control server to download the public key. The private key is accessible only to the criminals who wrote the CryptoLocker software. Usually, the victim has no more than 72 hours to pay the ransom before their private key is deleted forever, and it is impossible to decrypt any files without this key.
So you have to think about prevention first. Most antivirus software already includes a component that helps to identify a ransomware threat in the early stages of infection, without occurring the loss of any sensitive data. It is important for users to ensure that this functionality is switched on in their antivirus solution. If you need help talk to our ransomware removal experts today
At Tier3 Cyber Security we are continuously working with other security companies and law enforcement agencies to identify as many keys as possible, for as many variants as possible. If you have some information that you think can help, please share it with us and if you need any help with removal of ransomware please send us email to [email protected]. All queries are dealt in confidence. You can also contact our ransomware removal experts to know more about ransomware protection products for your personal or business needs.

