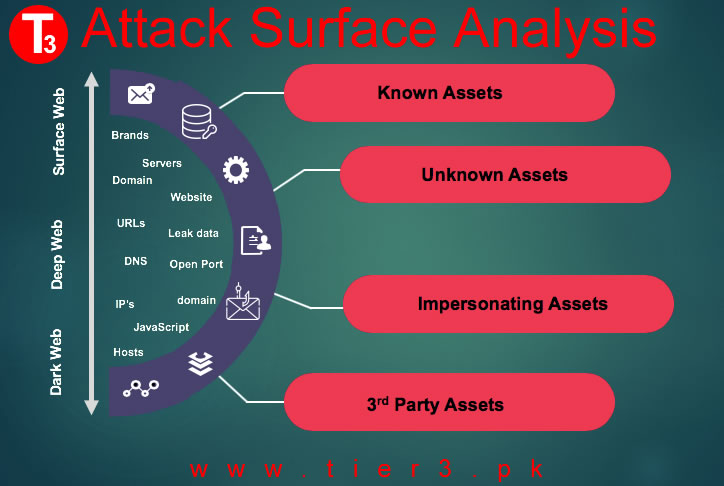
Tier3 Cyber security Attack Surface Analysis is about mapping out what parts of YOUR IT systems need to be reviewed and tested for security vulnerabilities. Our Attack Surface Analysis helps you to identify the functions and parts of the system your organisation needs to review and test for security vulnerabilities. The attack surface represents all the points where a potential attacker could target an organization’s network, systems, applications, or data. ASM services are essential for proactive cybersecurity, as they assist in reducing an organization’s exposure to cyber threats and vulnerabilities.
The attack surface of your system is all the vulnerabilities or weaknesses in the security controls that an attacker or hacker can exploit to cause harm to your organization and its IT systems. These are attack vectors used by the threat actors to gain unauthorized access to confidential data and carry out cyberattacks. For example, security gaps in IoT and smart devices, web applications, mobile devices, remote and VPN networks, data centers, supply chain, etc in Pakistan.
Tier3 Attack surface analysis applies a proactive risk-based approach which develops your organisation capabilities to predict and mitigate cyber attacks before they occur. In essence, Tier3 attack surface analysis answers four fundamental questions: what, where, when, and how of a cyberattack.
· What part of the infrastructure is vulnerable and what security controls are required.
· When the attack surface changes and what processes affects it.
· Where to apply defense-in-depth protection for your system and business processes.
· How to minimize risk and protect from cyberattacks .
Attack Surface management is an ongoing process. The external attack surface changes as an organization’s digital footprint evolves and new vulnerabilities are discovered. This necessitates regular monitoring, updates, and adjustments to ASM strategies.
Integration with Cyber threat intelligence feeds enables our ASM services to correlate discovered assets with known threats and indicators of compromise, helping organizations focus on the most critical risks.
- Strategic Cyber Threat Intelligence : It utilizes comprehensive pattern and emerging risk analysis to provide an outline of future cyber-attack implications.
- Operational Cyber Threat Intelligence : It is mainly used to make resource management decisions regarding actual and potential risks, historical resources, affiliations, and motives of threat actors.
- Tactical Cyber Threat Intelligence : Primarily, its main target is a technically trained audience and allows them to learn more specific details on threat actors’ tactics, techniques, and procedures (TTPs).
- Technical Cyber Threat Intelligence : It focuses on the technological details suggesting a cyber-security threat, such as phishing email lines or malicious URLs.
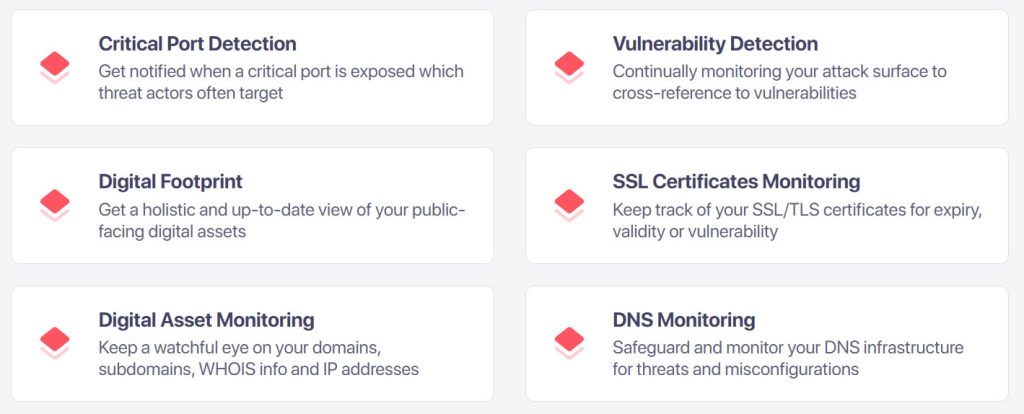
Tier3 Attack surface analysis incorporates Vulnerability assessment and management to find and fix security vulnerabilities, counter new security threats, and make the environment less susceptible to attack. We also, apply threat modeling and attack simulations to correctly identify, categorize, and mitigate cyber risks. As attacks can from both inside and outside the organization, hence the zero-trust model is followed to tremendously reduce the attack surface. Using this Zero trust least-privilege strategy, network segmentation, and enforces strict access control we consequently deny malicious actors ability to easily move laterally inside your network and exfiltrate data.
Attack Surface Management
Tier3 Attack Surface Management (ASM) services help users gain additional visibility and context regarding the severity of unknown external-facing and internal digital assets in an automated manner. Our ASM services are invaluable for organizations looking to strengthen their security posture, reduce the risk of cyberattacks, and enhance their incident response capabilities. By gaining a comprehensive view of their attack surface and proactively addressing vulnerabilities and threats, organizations can effectively manage their digital risk and protect their critical assets.
Need more information, contact our experts to discuss more.


