US bank account holders more likely to switch after fraud
February 20, 2017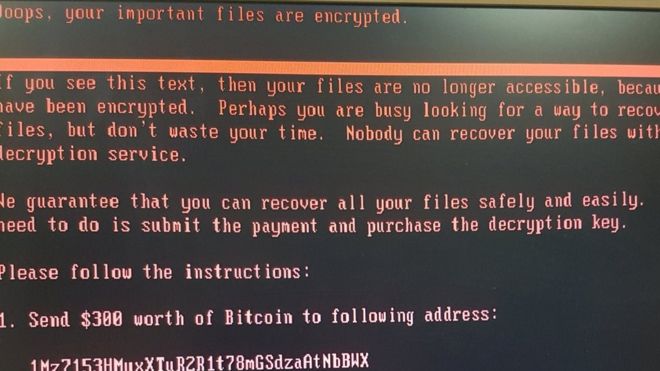
How easy it is for criminals to exploit your organisation using ransomware ?
February 21, 2017Duqu Malware – Analysis
Duqu 2.0 is a really impressive piece of malware, related to Stuxnet and probably written by the NSA. One of its security features is that it stays resident in its host’s memory without ever writing persistent files to the system’s drives. Now, this same technique is being used by criminals:
Now, fileless malware is going mainstream, as financially motivated criminal hackers mimic their nation-sponsored counterparts. According to research Kaspersky Lab plans to publish Wednesday, networks belonging to at least 140 banks and other enterprises have been infected by malware that relies on the same in-memory design to remain nearly invisible.
Because infections are so hard to spot, the actual number is likely much higher. Another trait that makes the infections hard to detect is the use of legitimate and widely used system administrative and security tools — like PowerShell, Metasploit, and Mimikatz — to inject the malware.
The researchers had first discovered the malware late last year, when a bank’s security team found a copy of Meterpreter — an in-memory component of Metasploit — residing inside the physical memory of a Microsoft domain controller.
After conducting a forensic analysis, the researchers found that the Meterpreter code was downloaded and injected into memory using PowerShell commands. The infected machine also used Microsoft’s NETSH networking tool to transport data to attacker-controlled servers.
To obtain the administrative privileges necessary to do these things, the attackers also relied on Mimikatz. To reduce the evidence left in logs or hard drives, the attackers stashed the PowerShell commands into the Windows registry.
If you are infected with Duqu or are victim of cyber crime or hacking please contact Tier3 Cyber Security Cert Team.