Email Marketing Software – Developed for Pakistan Supports Urdu Language
March 15, 2017Federal Investigation Agency (FIA) confirms one arrest in Social media Blasphemy case
March 22, 2017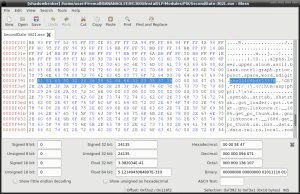
Cyber security professionals have discovered two recent fileless malware campaigns targeting financial institutions, government agencies and other enterprises are linked to the same attack group.
The campaigns, disclosed by Kaspersky Lab and Cisco’s Talos research outfit in the last five weeks, made extensive use of fileless malware and known penetration testing tools and utilities to spy on organizations and move data and money off of networks.
Researchers at Israeli security company Morphisec said today that in investigating a recent campaign, they discovered the framework used to deliver the DNS PowerShell Messenger attacks reported by Cisco and a similar attack uncovered by Kaspersky Lab that used Meterpreter and other known utilities against 140 banks worldwide.
The Meterpreter attacks, Kaspersky Lab said, could be connected to the GCMAN and Carbanak groups, which were responsible for $1 billion in thefts from financial institutions, according to a 2015 report.
FireEye calls this group FIN7 and said it was targeting individuals involved in SEC filings.
The framework has since disappeared online following a brief interaction with the attacker and researchers. Omri Dotan of Morphisec said the researchers attempted to build some trust with the attacker and tried to communicate in Russian before he disabled the command and control infrastructure and removed the framework.
“There is a high level of probability that we have attributed a whole bunch of attacks across the globe to one actor and this platform,” Dotan said. “Through this [interaction] we had with them, they took it down and quite likely disrupted any ongoing attacks. Now they are going to have to rebuild it and do this stuff over from scratch.”
Researches said in an analysis published today that on March 8 during an investigation into an attack against several high-profile enterprises, it found the framework used to deliver a number of variations of attacks, all of which leave no artifacts on the compromised machines. These artifacts either match, or are similar to, others used in the attacks described by Kaspersky and Cisco, they said.
The attacks begin with phishing emails targeting organizations using a Word document that is protected, which urges the user to enable the content. By doing so, the victim executes a macro embedded in the document that executes a PowerShell command using Windows Management Instrumentation, infrastructure used to automate tasks on remote machines.
A PowerShell script called Updater.ps1 is enabled that opens a backdoor and grabs commands from the command and control server. It also lowers security restrictions around macros so that more macro-based documents can be sent and will execute without user interaction. Researchers found additional scripts on the command and control server that execute Mimikatz, which is used to extract passwords and hashes from memory, LaZagne, a open source application used to retrieve credentials stored on a local hard drive, and DNS Messenger.
They had access to the command and control server for three days and was able fingerprint a number of artifacts on the framework, encryption routines and IP addresses that led them to conclude the likely connection with other similar attacks.
“At some point toward the end of our investigation the attacker contacted our people through the shellcode. We had a brief interaction where our folks tried to lure the hacker to reveal part of his identity,” Dotan said. “At some point, we tried to talk to them in Russian, but at that point, he asked for ‘English, please.’ He then started to shut down the command and control server and completely took down the platform.”