Afghan diplomats in Pakistan suspicious of targeted “Cyber attacks” by state-backed APT Groups
May 26, 2018Bank Islami denies losing $6 million in country’s ‘biggest cyber attack’
October 30, 2018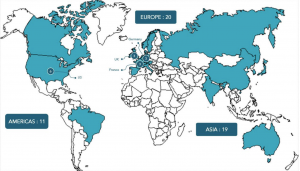
The Pakistani hacker group is attempting to attack government organizations using the infrastructure it also uses to send spam to malware.
According to researchers from Palo Alto Networks Unit 42, the group Gorgon Group is active since February this year and with the help of targeted phishing attacks government agencies in Spain, Britain, the US and Russia. In the disclosure of a malicious campaign, experts were helped by the use of hackers popular URL reduction service, through which they were able to obtain data on the number of clicks on links and other information related to Gorgon Group.
Attackers send phishing emails to their victims on issues of terrorism, as well as military and political problems in Pakistan and neighboring countries. Emails contain Microsoft Word documents with an exploit for the CVE-2017-0199 vulnerability. When the victim opens the document, a script on Visual Basic with PowerShell commands is downloaded to the computer, after which the attacker can execute commands and download malicious software onto the compromised system.
In the case of Gorgon Group, one of the three Trojan families for stealing data and espionage is installed on hacked PCs – NanoCoreRAT, QuasarRAT or NJRAT.
The exact number of successful infections is unknown. Nevertheless, the researchers found evidence that even a campaign with such a primitive infrastructure could pose a threat to the security of government organizations.
Source: https://www.securitylab.ru/news/494778.php